Nigx的修改弱密码套件
目录
各协议对应的密码套件名称:
Nmap &Sslscan查询密码套件
Nigx修改弱密码套件
1. MD5、DES和CBC\_SHA类型修改
- 限制很多的特定类型密码套件
Windows Server系统的协议修改
1. 各协议对应的密码套件名称:
以下列表给出了相关规范中的 SSL 或 TLS 密码套件名称及其 OpenSSL 等效项。应该注意的是,一些密码套件名称不包括使用的身份验证,例如 DES-CBC3-SHA。在这些情况下,将使用 RSA 身份验证。
SSL v3.0 密码套件。
SSL_RSA_WITH_NULL_MD5 NULL-MD5 SSL_RSA_WITH_NULL_SHA NULL-SHA SSL_RSA_EXPORT_WITH_RC4_40_MD5 EXP-RC4-MD5 SSL_RSA_WITH_RC4_128_MD5 RC4-MD5 SSL_RSA_WITH_RC4_128_SHA RC4-SHA SSL_RSA_EXPORT_WITH_RC2_CBC_40_MD5 EXP-RC2-CBC-MD5 SSL_RSA_WITH_IDEA_CBC_SHA IDEA-CBC-SHA SSL_RSA_EXPORT_WITH_DES40_CBC_SHA EXP-DES-CBC-SHA SSL_RSA_WITH_DES_CBC_SHA DES-CBC-SHA SSL_RSA_WITH_3DES_EDE_CBC_SHA DES-CBC3-SHA SSL_DH_DSS_WITH_DES_CBC_SHA DH-DSS-DES-CBC-SHA SSL_DH_DSS_WITH_3DES_EDE_CBC_SHA DH-DSS-DES-CBC3-SHA SSL_DH_RSA_WITH_DES_CBC_SHA DH-RSA-DES-CBC-SHA SSL_DH_RSA_WITH_3DES_EDE_CBC_SHA DH-RSA-DES-CBC3-SHA SSL_DHE_DSS_EXPORT_WITH_DES40_CBC_SHA EXP-EDH-DSS-DES-CBC-SHA SSL_DHE_DSS_WITH_DES_CBC_SHA EDH-DSS-CBC-SHA SSL_DHE_DSS_WITH_3DES_EDE_CBC_SHA EDH-DSS-DES-CBC3-SHA SSL_DHE_RSA_EXPORT_WITH_DES40_CBC_SHA EXP-EDH-RSA-DES-CBC-SHA SSL_DHE_RSA_WITH_DES_CBC_SHA EDH-RSA-DES-CBC-SHA SSL_DHE_RSA_WITH_3DES_EDE_CBC_SHA EDH-RSA-DES-CBC3-SHA SSL_DH_anon_EXPORT_WITH_RC4_40_MD5 EXP-ADH-RC4-MD5 SSL_DH_anon_WITH_RC4_128_MD5 ADH-RC4-MD5 SSL_DH_anon_EXPORT_WITH_DES40_CBC_SHA EXP-ADH-DES-CBC-SHA SSL_DH_anon_WITH_DES_CBC_SHA ADH-DES-CBC-SHA SSL_DH_anon_WITH_3DES_EDE_CBC_SHA ADH-DES-CBC3-SHA SSL_FORTEZZA_KEA_WITH_NULL_SHA Not implemented. SSL_FORTEZZA_KEA_WITH_FORTEZZA_CBC_SHA Not implemented. SSL_FORTEZZA_KEA_WITH_RC4_128_SHA Not implemented.
TLS v1.0 密码套件。
TLS_RSA_WITH_NULL_MD5 NULL-MD5 TLS_RSA_WITH_NULL_SHA NULL-SHA TLS_RSA_EXPORT_WITH_RC4_40_MD5 EXP-RC4-MD5 TLS_RSA_WITH_RC4_128_MD5 RC4-MD5 TLS_RSA_WITH_RC4_128_SHA RC4-SHA TLS_RSA_EXPORT_WITH_RC2_CBC_40_MD5 EXP-RC2-CBC-MD5 TLS_RSA_WITH_IDEA_CBC_SHA IDEA-CBC-SHA TLS_RSA_EXPORT_WITH_DES40_CBC_SHA EXP-DES-CBC-SHA TLS_RSA_WITH_DES_CBC_SHA DES-CBC-SHA TLS_RSA_WITH_3DES_EDE_CBC_SHA DES-CBC3-SHA TLS_DH_DSS_EXPORT_WITH_DES40_CBC_SHA Not implemented. TLS_DH_DSS_WITH_DES_CBC_SHA Not implemented. TLS_DH_DSS_WITH_3DES_EDE_CBC_SHA Not implemented. TLS_DH_RSA_EXPORT_WITH_DES40_CBC_SHA Not implemented. TLS_DH_RSA_WITH_DES_CBC_SHA Not implemented. TLS_DH_RSA_WITH_3DES_EDE_CBC_SHA Not implemented. TLS_DHE_DSS_EXPORT_WITH_DES40_CBC_SHA EXP-EDH-DSS-DES-CBC-SHA TLS_DHE_DSS_WITH_DES_CBC_SHA EDH-DSS-CBC-SHA TLS_DHE_DSS_WITH_3DES_EDE_CBC_SHA EDH-DSS-DES-CBC3-SHA TLS_DHE_RSA_EXPORT_WITH_DES40_CBC_SHA EXP-EDH-RSA-DES-CBC-SHA TLS_DHE_RSA_WITH_DES_CBC_SHA EDH-RSA-DES-CBC-SHA TLS_DHE_RSA_WITH_3DES_EDE_CBC_SHA EDH-RSA-DES-CBC3-SHA TLS_DH_anon_EXPORT_WITH_RC4_40_MD5 EXP-ADH-RC4-MD5 TLS_DH_anon_WITH_RC4_128_MD5 ADH-RC4-MD5 TLS_DH_anon_EXPORT_WITH_DES40_CBC_SHA EXP-ADH-DES-CBC-SHA TLS_DH_anon_WITH_DES_CBC_SHA ADH-DES-CBC-SHA TLS_DH_anon_WITH_3DES_EDE_CBC_SHA ADH-DES-CBC3-SHA
来自 RFC3268 的 AES 密码套件,扩展了 TLS v1.0
TLS_RSA_WITH_AES_128_CBC_SHA AES128-SHA TLS_RSA_WITH_AES_256_CBC_SHA AES256-SHA TLS_DH_DSS_WITH_AES_128_CBC_SHA DH-DSS-AES128-SHA TLS_DH_DSS_WITH_AES_256_CBC_SHA DH-DSS-AES256-SHA TLS_DH_RSA_WITH_AES_128_CBC_SHA DH-RSA-AES128-SHA TLS_DH_RSA_WITH_AES_256_CBC_SHA DH-RSA-AES256-SHA TLS_DHE_DSS_WITH_AES_128_CBC_SHA DHE-DSS-AES128-SHA TLS_DHE_DSS_WITH_AES_256_CBC_SHA DHE-DSS-AES256-SHA TLS_DHE_RSA_WITH_AES_128_CBC_SHA DHE-RSA-AES128-SHA TLS_DHE_RSA_WITH_AES_256_CBC_SHA DHE-RSA-AES256-SHA TLS_DH_anon_WITH_AES_128_CBC_SHA ADH-AES128-SHA TLS_DH_anon_WITH_AES_256_CBC_SHA ADH-AES256-SHA
来自 RFC4132 的 Camellia 密码套件,扩展了 TLS v1.0
TLS_RSA_WITH_CAMELLIA_128_CBC_SHA CAMELLIA128-SHA TLS_RSA_WITH_CAMELLIA_256_CBC_SHA CAMELLIA256-SHA TLS_DH_DSS_WITH_CAMELLIA_128_CBC_SHA DH-DSS-CAMELLIA128-SHA TLS_DH_DSS_WITH_CAMELLIA_256_CBC_SHA DH-DSS-CAMELLIA256-SHA TLS_DH_RSA_WITH_CAMELLIA_128_CBC_SHA DH-RSA-CAMELLIA128-SHA TLS_DH_RSA_WITH_CAMELLIA_256_CBC_SHA DH-RSA-CAMELLIA256-SHA TLS_DHE_DSS_WITH_CAMELLIA_128_CBC_SHA DHE-DSS-CAMELLIA128-SHA TLS_DHE_DSS_WITH_CAMELLIA_256_CBC_SHA DHE-DSS-CAMELLIA256-SHA TLS_DHE_RSA_WITH_CAMELLIA_128_CBC_SHA DHE-RSA-CAMELLIA128-SHA TLS_DHE_RSA_WITH_CAMELLIA_256_CBC_SHA DHE-RSA-CAMELLIA256-SHA TLS_DH_anon_WITH_CAMELLIA_128_CBC_SHA ADH-CAMELLIA128-SHA TLS_DH_anon_WITH_CAMELLIA_256_CBC_SHA ADH-CAMELLIA256-SHA
来自 RFC4162 的 SEED 密码套件,扩展了 TLS v1.0
TLS_RSA_WITH_SEED_CBC_SHA SEED-SHA TLS_DH_DSS_WITH_SEED_CBC_SHA DH-DSS-SEED-SHA TLS_DH_RSA_WITH_SEED_CBC_SHA DH-RSA-SEED-SHA TLS_DHE_DSS_WITH_SEED_CBC_SHA DHE-DSS-SEED-SHA TLS_DHE_RSA_WITH_SEED_CBC_SHA DHE-RSA-SEED-SHA TLS_DH_anon_WITH_SEED_CBC_SHA ADH-SEED-SHA
来自 Draft-chudov-cryptopro-cptls 的 GOST 密码套件,扩展了 TLS v1.0
注意:这些密码需要一个包含 GOST 加密算法的引擎,例如OpenSSL 发行版中包含的ccgost引擎。
TLS_GOSTR341094_WITH_28147_CNT_IMIT GOST94-GOST89-GOST89 TLS_GOSTR341001_WITH_28147_CNT_IMIT GOST2001-GOST89-GOST89 TLS_GOSTR341094_WITH_NULL_GOSTR3411 GOST94-NULL-GOST94 TLS_GOSTR341001_WITH_NULL_GOSTR3411 GOST2001-NULL-GOST94
额外的 Export 1024 和其他密码套件
注意:这些密码也可用于 SSL v3。
TLS_RSA_EXPORT1024_WITH_DES_CBC_SHA EXP1024-DES-CBC-SHA TLS_RSA_EXPORT1024_WITH_RC4_56_SHA EXP1024-RC4-SHA TLS_DHE_DSS_EXPORT1024_WITH_DES_CBC_SHA EXP1024-DHE-DSS-DES-CBC-SHA TLS_DHE_DSS_EXPORT1024_WITH_RC4_56_SHA EXP1024-DHE-DSS-RC4-SHA TLS_DHE_DSS_WITH_RC4_128_SHA DHE-DSS-RC4-SHA
椭圆曲线密码套件。
TLS_ECDH_RSA_WITH_NULL_SHA ECDH-RSA-NULL-SHA TLS_ECDH_RSA_WITH_RC4_128_SHA ECDH-RSA-RC4-SHA TLS_ECDH_RSA_WITH_3DES_EDE_CBC_SHA ECDH-RSA-DES-CBC3-SHA TLS_ECDH_RSA_WITH_AES_128_CBC_SHA ECDH-RSA-AES128-SHA TLS_ECDH_RSA_WITH_AES_256_CBC_SHA ECDH-RSA-AES256-SHA TLS_ECDH_ECDSA_WITH_NULL_SHA ECDH-ECDSA-NULL-SHA TLS_ECDH_ECDSA_WITH_RC4_128_SHA ECDH-ECDSA-RC4-SHA TLS_ECDH_ECDSA_WITH_3DES_EDE_CBC_SHA ECDH-ECDSA-DES-CBC3-SHA TLS_ECDH_ECDSA_WITH_AES_128_CBC_SHA ECDH-ECDSA-AES128-SHA TLS_ECDH_ECDSA_WITH_AES_256_CBC_SHA ECDH-ECDSA-AES256-SHA TLS_ECDHE_RSA_WITH_NULL_SHA ECDHE-RSA-NULL-SHA TLS_ECDHE_RSA_WITH_RC4_128_SHA ECDHE-RSA-RC4-SHA TLS_ECDHE_RSA_WITH_3DES_EDE_CBC_SHA ECDHE-RSA-DES-CBC3-SHA TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA ECDHE-RSA-AES128-SHA TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA ECDHE-RSA-AES256-SHA TLS_ECDHE_ECDSA_WITH_NULL_SHA ECDHE-ECDSA-NULL-SHA TLS_ECDHE_ECDSA_WITH_RC4_128_SHA ECDHE-ECDSA-RC4-SHA TLS_ECDHE_ECDSA_WITH_3DES_EDE_CBC_SHA ECDHE-ECDSA-DES-CBC3-SHA TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA ECDHE-ECDSA-AES128-SHA TLS_ECDHE_ECDSA_WITH_AES_256_CBC_SHA ECDHE-ECDSA-AES256-SHA TLS_ECDH_anon_WITH_NULL_SHA AECDH-NULL-SHA TLS_ECDH_anon_WITH_RC4_128_SHA AECDH-RC4-SHA TLS_ECDH_anon_WITH_3DES_EDE_CBC_SHA AECDH-DES-CBC3-SHA TLS_ECDH_anon_WITH_AES_128_CBC_SHA AECDH-AES128-SHA TLS_ECDH_anon_WITH_AES_256_CBC_SHA AECDH-AES256-SHA
TLS v1.2 密码套件
TLS_RSA_WITH_NULL_SHA256 NULL-SHA256 TLS_RSA_WITH_AES_128_CBC_SHA256 AES128-SHA256 TLS_RSA_WITH_AES_256_CBC_SHA256 AES256-SHA256 TLS_RSA_WITH_AES_128_GCM_SHA256 AES128-GCM-SHA256 TLS_RSA_WITH_AES_256_GCM_SHA384 AES256-GCM-SHA384 TLS_DH_RSA_WITH_AES_128_CBC_SHA256 DH-RSA-AES128-SHA256 TLS_DH_RSA_WITH_AES_256_CBC_SHA256 DH-RSA-AES256-SHA256 TLS_DH_RSA_WITH_AES_128_GCM_SHA256 DH-RSA-AES128-GCM-SHA256 TLS_DH_RSA_WITH_AES_256_GCM_SHA384 DH-RSA-AES256-GCM-SHA384 TLS_DH_DSS_WITH_AES_128_CBC_SHA256 DH-DSS-AES128-SHA256 TLS_DH_DSS_WITH_AES_256_CBC_SHA256 DH-DSS-AES256-SHA256 TLS_DH_DSS_WITH_AES_128_GCM_SHA256 DH-DSS-AES128-GCM-SHA256 TLS_DH_DSS_WITH_AES_256_GCM_SHA384 DH-DSS-AES256-GCM-SHA384 TLS_DHE_RSA_WITH_AES_128_CBC_SHA256 DHE-RSA-AES128-SHA256 TLS_DHE_RSA_WITH_AES_256_CBC_SHA256 DHE-RSA-AES256-SHA256 TLS_DHE_RSA_WITH_AES_128_GCM_SHA256 DHE-RSA-AES128-GCM-SHA256 TLS_DHE_RSA_WITH_AES_256_GCM_SHA384 DHE-RSA-AES256-GCM-SHA384 TLS_DHE_DSS_WITH_AES_128_CBC_SHA256 DHE-DSS-AES128-SHA256 TLS_DHE_DSS_WITH_AES_256_CBC_SHA256 DHE-DSS-AES256-SHA256 TLS_DHE_DSS_WITH_AES_128_GCM_SHA256 DHE-DSS-AES128-GCM-SHA256 TLS_DHE_DSS_WITH_AES_256_GCM_SHA384 DHE-DSS-AES256-GCM-SHA384 TLS_ECDH_RSA_WITH_AES_128_CBC_SHA256 ECDH-RSA-AES128-SHA256 TLS_ECDH_RSA_WITH_AES_256_CBC_SHA384 ECDH-RSA-AES256-SHA384 TLS_ECDH_RSA_WITH_AES_128_GCM_SHA256 ECDH-RSA-AES128-GCM-SHA256 TLS_ECDH_RSA_WITH_AES_256_GCM_SHA384 ECDH-RSA-AES256-GCM-SHA384 TLS_ECDH_ECDSA_WITH_AES_128_CBC_SHA256 ECDH-ECDSA-AES128-SHA256 TLS_ECDH_ECDSA_WITH_AES_256_CBC_SHA384 ECDH-ECDSA-AES256-SHA384 TLS_ECDH_ECDSA_WITH_AES_128_GCM_SHA256 ECDH-ECDSA-AES128-GCM-SHA256 TLS_ECDH_ECDSA_WITH_AES_256_GCM_SHA384 ECDH-ECDSA-AES256-GCM-SHA384 TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA256 ECDHE-RSA-AES128-SHA256 TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA384 ECDHE-RSA-AES256-SHA384 TLS_ECDHE_RSA_WITH_AES_128_GCM_SHA256 ECDHE-RSA-AES128-GCM-SHA256 TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384 ECDHE-RSA-AES256-GCM-SHA384 TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA256 ECDHE-ECDSA-AES128-SHA256 TLS_ECDHE_ECDSA_WITH_AES_256_CBC_SHA384 ECDHE-ECDSA-AES256-SHA384 TLS_ECDHE_ECDSA_WITH_AES_128_GCM_SHA256 ECDHE-ECDSA-AES128-GCM-SHA256 TLS_ECDHE_ECDSA_WITH_AES_256_GCM_SHA384 ECDHE-ECDSA-AES256-GCM-SHA384 TLS_DH_anon_WITH_AES_128_CBC_SHA256 ADH-AES128-SHA256 TLS_DH_anon_WITH_AES_256_CBC_SHA256 ADH-AES256-SHA256 TLS_DH_anon_WITH_AES_128_GCM_SHA256 ADH-AES128-GCM-SHA256 TLS_DH_anon_WITH_AES_256_GCM_SHA384 ADH-AES256-GCM-SHA384
预共享密钥 (PSK) 密码
TLS_PSK_WITH_RC4_128_SHA PSK-RC4-SHA TLS_PSK_WITH_3DES_EDE_CBC_SHA PSK-3DES-EDE-CBC-SHA TLS_PSK_WITH_AES_128_CBC_SHA PSK-AES128-CBC-SHA TLS_PSK_WITH_AES_256_CBC_SHA PSK-AES256-CBC-SHA
已弃用的 SSL v2.0 密码套件。
SSL_CK_RC4_128_WITH_MD5 RC4-MD5 SSL_CK_RC4_128_EXPORT40_WITH_MD5 Not implemented. SSL_CK_RC2_128_CBC_WITH_MD5 RC2-CBC-MD5 SSL_CK_RC2_128_CBC_EXPORT40_WITH_MD5 Not implemented. SSL_CK_IDEA_128_CBC_WITH_MD5 IDEA-CBC-MD5 SSL_CK_DES_64_CBC_WITH_MD5 Not implemented. SSL_CK_DES_192_EDE3_CBC_WITH_MD5 DES-CBC3-MD5
2. Nmap &Sslscan查询密码套件
root@Fkali:~/Desktop#nmap —script ssl-enum-ciphers -p 443 域名地址(baidu.com)
Starting Nmap 7.91 ( https://nmap.org ) at 2021-06-08 16:07 HKT
Nmap scan report for ****.com (0.0.0.0)
Host is up (0.0022s latency).PORT STATE SERVICE
443/tcp open https
| ssl-enum-ciphers:
| TLSv1.2:
| ciphers:
| TLS_ECDHE_RSA_WITH_AES_128_GCM_SHA256 (ecdh_x25519) - A
| TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384 (ecdh_x25519) - A
| TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA256 (ecdh_x25519) - A
| TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA384 (ecdh_x25519) - A
| TLS_RSA_WITH_AES_128_GCM_SHA256 (rsa 2048) - A
| TLS_RSA_WITH_AES_256_GCM_SHA384 (rsa 2048) - A
| TLS_RSA_WITH_AES_128_CBC_SHA256 (rsa 2048) - A
| TLS_RSA_WITH_AES_256_CBC_SHA256 (rsa 2048) - A
| TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA (ecdh_x25519) - A
| TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA (ecdh_x25519) - A
| TLS_RSA_WITH_AES_128_CBC_SHA (rsa 2048) - A
| TLS_RSA_WITH_AES_256_CBC_SHA (rsa 2048) - A
| compressors:
| NULL
| cipher preference: server
|_ least strength: ANmap done: 1 IP address (1 host up) scanned in 1.78 seconds
root@Fkali:~/Desktop# sslscan -p 443 域名地址(baidu.com)
Version: 2.0.9-static
OpenSSL 1.1.1l-dev xx XXX xxxxConnected to *.*.*.*
Testing SSL server patchtest.gaiaworkforce.com on port 443 using SNI name patchtest.gaiaworkforce.com
SSL/TLS Protocols:
SSLv2 disabled
SSLv3 disabled
TLSv1.0 disabled
TLSv1.1 disabled
TLSv1.2 enabled
TLSv1.3 disabledTLS Fallback SCSV:
Server supports TLS Fallback SCSVTLS renegotiation:
Session renegotiation not supportedTLS Compression:
Compression disabledHeartbleed:
TLSv1.2 not vulnerable to heartbleedSupported Server Cipher(s):
Preferred TLSv1.2 128 bits ECDHE-RSA-AES128-GCM-SHA256 Curve 25519 DHE 253
Accepted TLSv1.2 256 bits ECDHE-RSA-AES256-GCM-SHA384 Curve 25519 DHE 253
Accepted TLSv1.2 128 bits ECDHE-RSA-AES128-SHA256 Curve 25519 DHE 253
Accepted TLSv1.2 256 bits ECDHE-RSA-AES256-SHA384 Curve 25519 DHE 253
Accepted TLSv1.2 128 bits AES128-GCM-SHA256
Accepted TLSv1.2 256 bits AES256-GCM-SHA384
Accepted TLSv1.2 128 bits AES128-SHA256
Accepted TLSv1.2 256 bits AES256-SHA256
Accepted TLSv1.2 128 bits ECDHE-RSA-AES128-SHA Curve 25519 DHE 253
Accepted TLSv1.2 256 bits ECDHE-RSA-AES256-SHA Curve 25519 DHE 253
Accepted TLSv1.2 128 bits AES128-SHA
Accepted TLSv1.2 256 bits AES256-SHAServer Key Exchange Group(s):
TLSv1.2 128 bits secp256r1 (NIST P-256)
TLSv1.2 192 bits secp384r1 (NIST P-384)
TLSv1.2 260 bits secp521r1 (NIST P-521)
TLSv1.2 128 bits x25519
TLSv1.2 224 bits x448SSL Certificate:
Signature Algorithm: sha256WithRSAEncryption
RSA Key Strength: 2048Subject: *.*.com
Altnames: DNS:*.*.com, *.com
Issuer: GeoTrust CN RSA CA G1Not valid before: Jun 5 00:00:00 2020 GMT
Not valid after: Sep 4 12:00:00 2022 GMT
上面使用Nmap和sslscan本地用密令行的方式处理的,也可以用在线的链接 //myssl.com/ssl.html, 但不建议这么处理,别人的服务器怎么可能纯免费给你使用,你总的留的东西下来。至于留啥,嘿嘿,话不多说,…
//myssl.com/ssl.html, 但不建议这么处理,别人的服务器怎么可能纯免费给你使用,你总的留的东西下来。至于留啥,嘿嘿,话不多说,…
3. Nigx修改弱密码套件
1. MD5、DES和CBC_SHA类型修改
这类修改相对不怎么烦,只要修改禁止项就行(有点像协议黑名单):
listen 8020 ssl;——————————————————————————-域名端口
server_name *****.com; ——————————————————-域名地址
ssl_certificate ***.com.pem;———————————————-证书
ssl_certificate_key ****.key; ————————————————密钥
ssl_session_cache shared1m;
ssl_session_timeout 5m;
ssl_ciphers HIGH:!aNULL:!SHA:!MD5;—————————-限制密码套件
# ssl_ciphers HIGH:!aNULL:!CBC_SHA:!MD5;
ssl_prefer_server_ciphers on;
ssl_protocols TLSv1.2;————————————————————限制协议
location / {
proxy_set_header Host $host;
proxy_set_header X-Forwarded-Proto https;
proxy_connect_timeout 120;
proxy_read_timeout 120;
proxy_send_timeout 120;
proxy_pass http://127.0.0.1;
}
2. 限制很多的特定类型密码套件
前面Nmap和SSLSCAN扫描出来的黄色部分,有很多,如果按照上面第一种处理方式,基本上不可行,如果存在远程链接的情况的话,按照上面的处理后,远程链接可能失败,弹出链接失败的对话框所以建议采用白名单的方式来处理这些问题:
ssl_ciphers ECDHE-RSA-AES128-SHA256
ECDHE-RSA-AES128-GCM-SHA256
ECDHE-ECDSA-AES128-SHA256
ECDHE-ECDSA-AES128-GCM-SHA256:
ECDHE-ECDSA-AES256-GCM-SHA384;
你想要加哪些可以参考前面第一项关于各密码套件的。选择自己需要的,直接添加到上面就可以了。 然后用Nmap/SSlscan再次扫描确认:
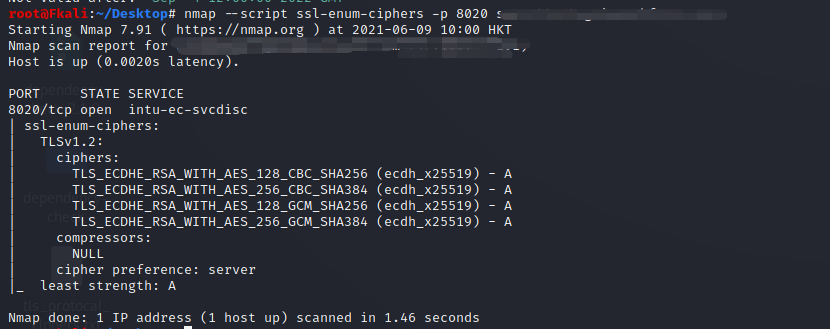
可以看到 ,通过上面的方式,已经处理成功了。
4. Windows Server系统的协议修改
关于windows Server系统端协议的修改可以参考之前的博客: [https://blog.csdn.net/m0\_37268841/article/details/99055258][https_blog.csdn.net_m0_37268841_article_details_99055258]



































还没有评论,来说两句吧...